Our Blogs and Insights
Discover insights, practical advice, and the latest trends in software, technology, design, and business, tailored for forward-thinking innovators.

Artificial Intelligence, IoT
Top 8 AIoT Trends Transforming IoT into Intelligent Systems of the Future
Artificial Intelligence
Building a Robust AI Ethics Framework: Best Practices and Implementation Guide for 2025

IoT, Smart Technology
IoT Wearables Chronic Disease: Transforming Real-Time Health Monitoring and Management

Artificial Intelligence, IoT
IoT in Healthcare: How Real-Time Monitoring is Transforming Patient Care

Artificial Intelligence, IoT
The Impact of IoT in Healthcare: Advancing Patient Care Through Interconnected Technology
Artificial Intelligence
Engineering a Sustainable Future: How Green Technology is Transforming Industries
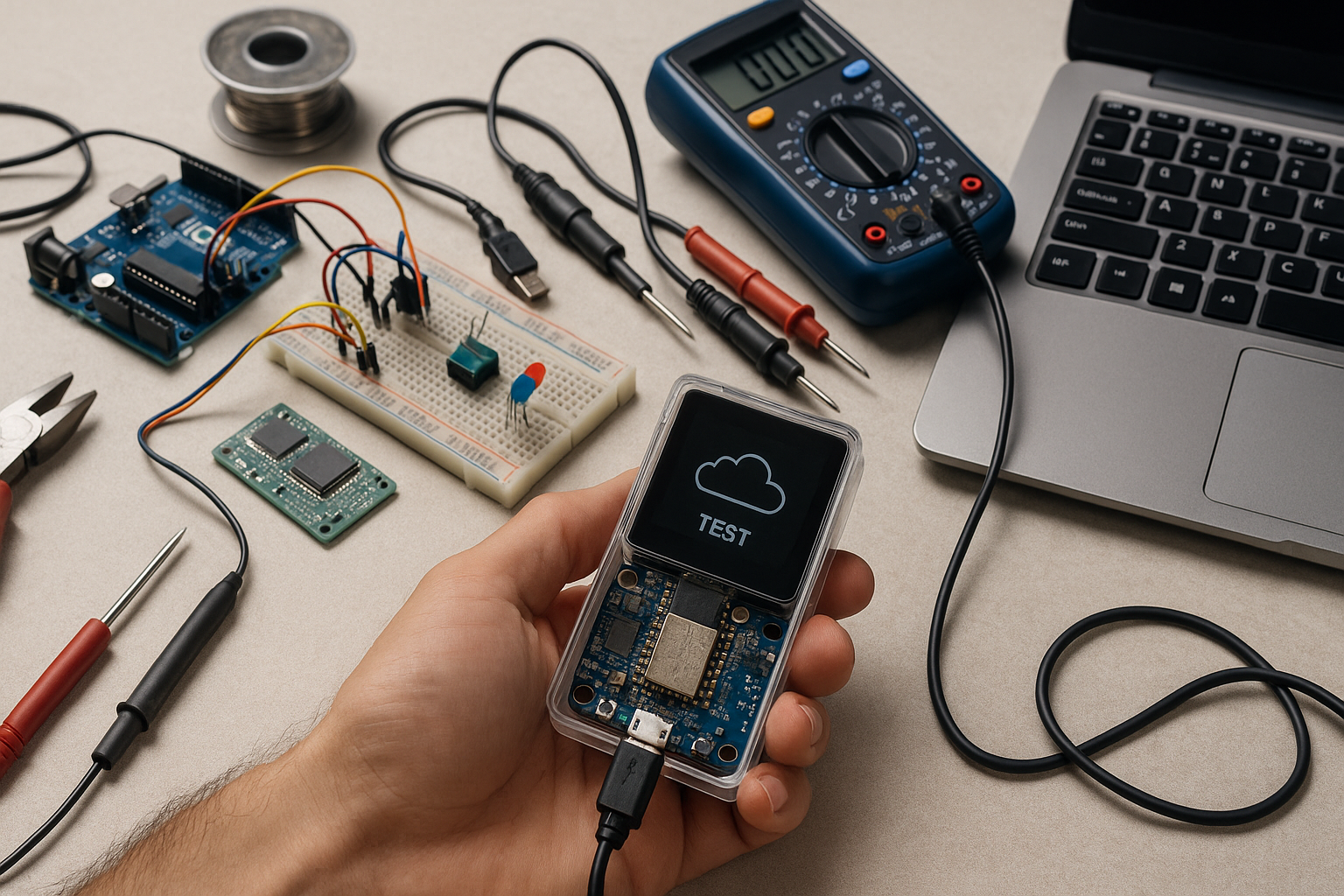
Artificial Intelligence
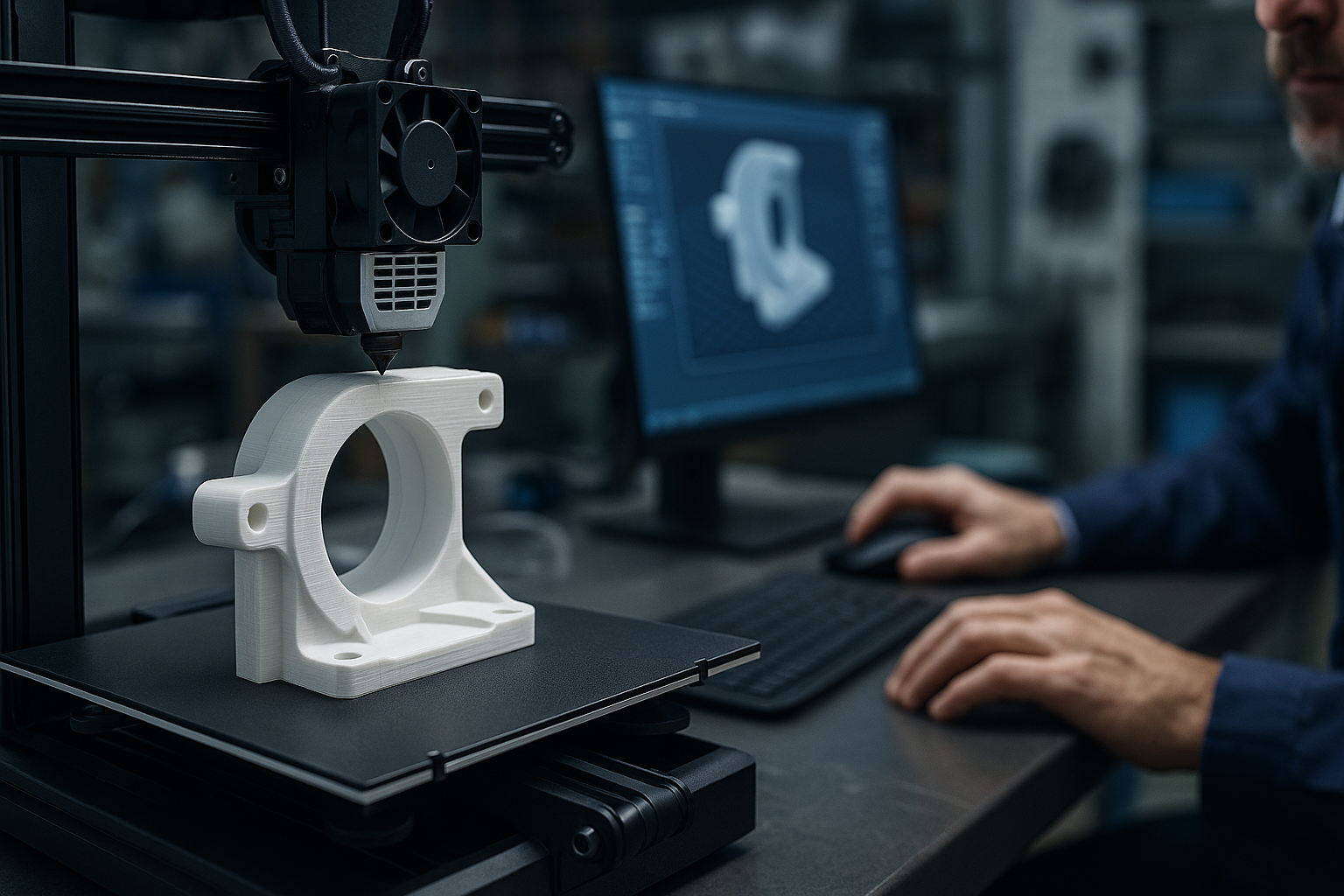
The Complete Guide to IoT Prototyping and Device Testing: A Step-by-Step Approach
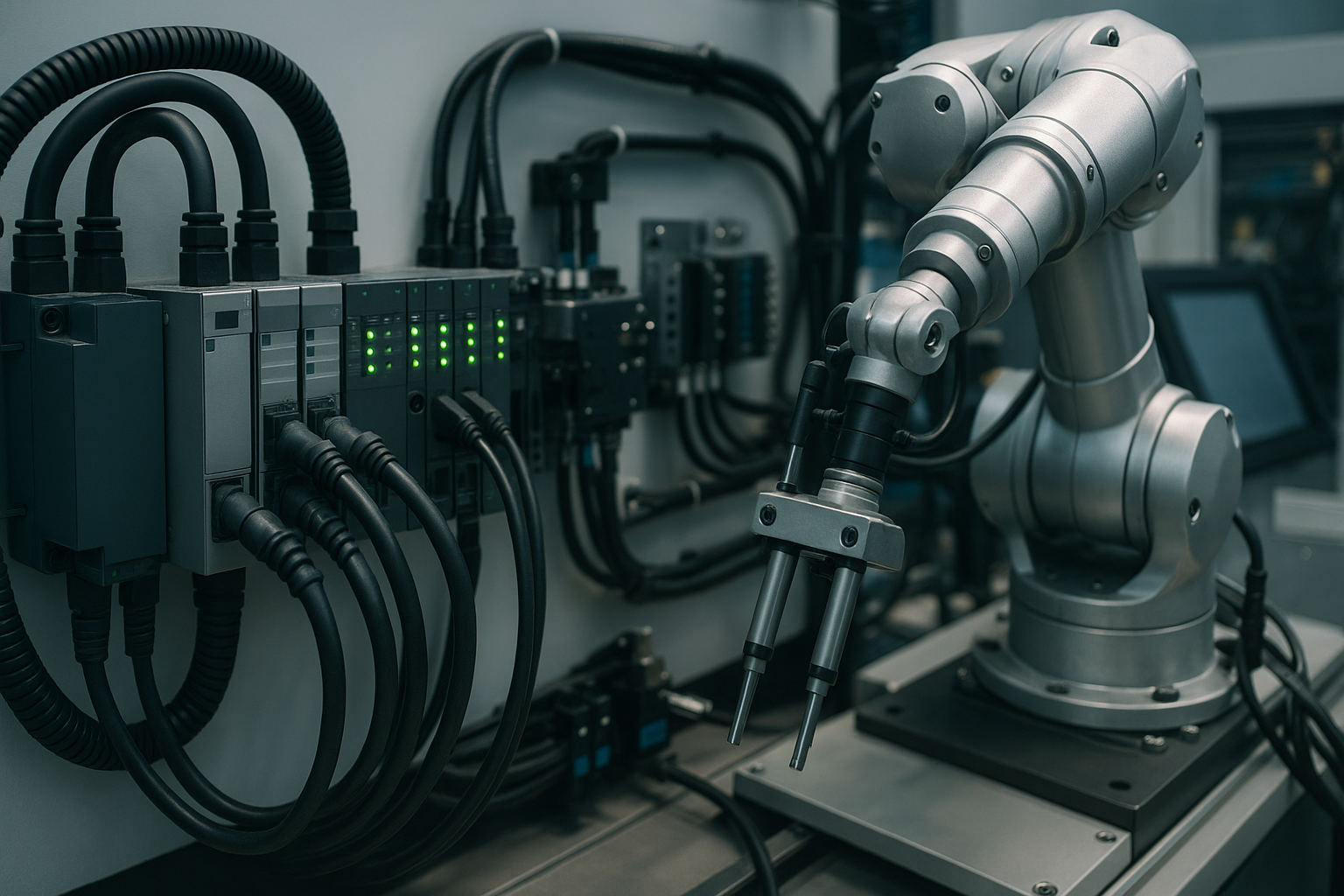
Artificial Intelligence, Engineering, IoT
Understanding Automation, A Guide to Systems, Services, and Implementation
Artificial Intelligence
AI Technology Trends for Enterprise: Transforming Software Development for the Future

Artificial Intelligence
AI Technology Trends for SMEs: How Small Software Teams Can Drive Innovation in 2025

Artificial Intelligence
AI Agents for Technical Troubleshooting: Supporting Costs and Service Quality

Artificial Intelligence
Building a Data-Driven Culture: Best Practices for Data Governance and Security

Artificial Intelligence, IoT
Advanced Robotics and Automation: 9 Emerging Trends Reshaping Industries
Artificial Intelligence
Multi-Agent Systems: Unlocking the Future of Collaborative AI and Its Transformative Impact
IoT, Software Development
IoT Platform Comparison: Amazon, Tuya, and Azure – Pros, Cons, and Technical Capabilities

Artificial Intelligence, IoT
The Future of Smart Security and Safety: Embracing AI + IoT Technologies